In order to thwart DDoS assaults, it’s critical to be aware of what drives the incident. Though DDoS assaults fluctuate drastically in mother nature when it comes to practices and solutions, DDoS attackers also could have a multitude of motives, including the pursuing.
After receiving our reply, you are able to attraction towards our final decision by getting in contact with Radware. We're going to critique your attraction and supply you with our remedy and our explanation of the reasons for our choice(s) inside of 60 days of obtaining it. We can even supply you with a link (to the extent readily available) in which you can submit a criticism to the relevant supervising authority.
We simply cannot reply to your request or offer you the requested personal information if we cannot validate your identification or authority to produce the ask for and ensure the personal details connected to you. We'll only use the personal details furnished with your ask for to confirm your identity or authority to create the ask for.
Exécution de la CLI : DAVOSET fournit une Answer fiable interface de ligne de commande qui vous aide à exécuter rapidement des attaques DDoS. Je l'ai testé et c'est le meilleur choix pour ceux qui préfileèhire une configuration sans tracas.
House your servers in state-of-the-art protected Data Centre located in Switzerland with our extremely skilled community and server engineers on web page.
Some attacks are completed by disgruntled persons and hacktivists eager to consider down an organization's servers just to create a statement, rejoice by exploiting cyber weakness, or Convey disapproval.
Such a attack can ddos web in essence shut down your internet site along with other data programs. An software-layer assault entails especially concentrating on vulnerabilities in widespread apps such as Home windows, Apache, or your World-wide-web server.
Yandex, August-September 2021: The Russian tech huge explained it managed “to repel a document attack of approximately 22 million requests per next,” introducing: “This is the biggest acknowledged attack within the historical past of the web”
At any time, you'll be able to decide-away from the collection of personal info by Radware’s assistance providers at: DPO@radware.com or datasubjectrights@radware.com or browsing the “notice of suitable to decide-out of the advertising or sharing of personal facts” webpage available at: .
Long-Time period Attack: An attack waged over a period of hrs or times is considered a long-expression assault. As an example, the DDoS assault on AWS caused disruption for three times ahead of last but not least getting mitigated.
As with all firewalls, a corporation can produce a list of rules that filter requests. They could begin with 1 set of procedures and after that modify them based on the things they notice as designs of suspicious exercise carried out via the DDoS.
Anytime a compromised technique calls home to your C&C server, it is said to get beaconing. This visitors passing in between a botnet member and its controller usually has distinct, exclusive styles and behaviors.
Remember to be suggested that login URL has altered likewise. You are able to regulate your account and orders by logging to the new user interface here. In the event you have any inquiries relating to this update, we are at your assistance 24/7. Study additional
A conventional DoS assault doesn’t use many, distributed products, nor will it give attention to gadgets between the attacker and also the Business. These assaults also are inclined not to employ numerous World wide web gadgets.
 Kel Mitchell Then & Now!
Kel Mitchell Then & Now!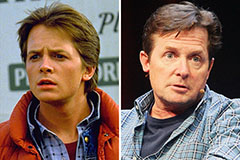 Michael J. Fox Then & Now!
Michael J. Fox Then & Now!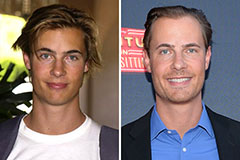 Erik von Detten Then & Now!
Erik von Detten Then & Now! Susan Dey Then & Now!
Susan Dey Then & Now! Kane Then & Now!
Kane Then & Now!